Inauthentic Accounts Are Spamming Twitter With Spyware That Can Steal Users’ Private Data
Twitter’s negligence is astounding

Background Information
Cybersecurity firm Trend Micro discovered Maikspy variants that were being distributed via numerous Twitter accounts in May 2018.
Maikspy initially posed as an adult game named after (former) adult film actress, Mia Khalifa, and first appeared on the Windows platform in December 2016 (Android variant appeared shortly thereafter in January 2017).
One of the Twitter accounts highlighted by Trend Micro was @RoundYear_Fun (account has since been suspended):
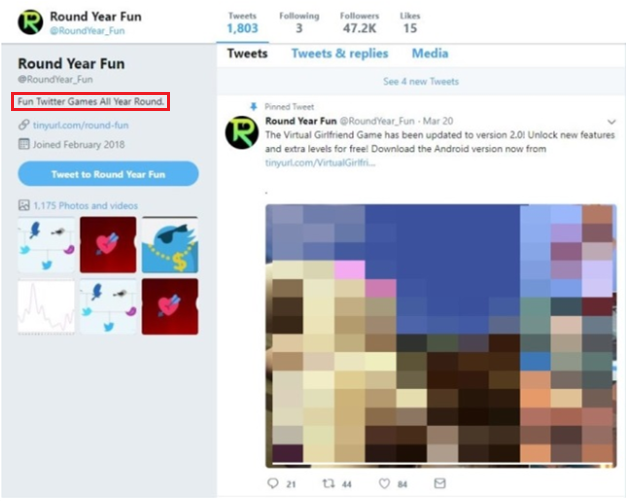
The cybersecurity firm identified several Twitter accounts promoting Virtual Girlfriend, an adult game, by linking to the malicious domain via short links:

After devices were infected (post downloading the Maikspy-carrying app, Virtual Girlfriend) the app’s routine included stealing the device’s phone number, installed app lists, contact lists, SMS messages, and more. The following were the supported commands discovered by Trend Micro:
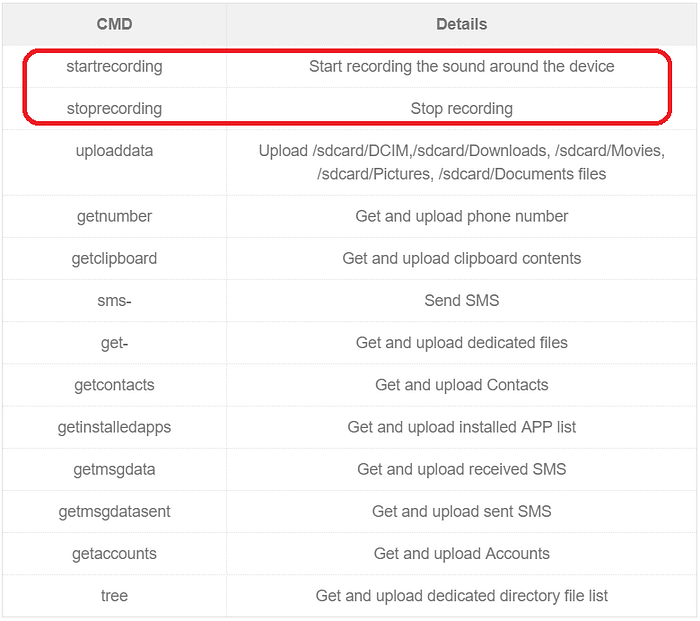
Maikspy is very nasty spyware — early variants, for example, were capable of recording phone calls.
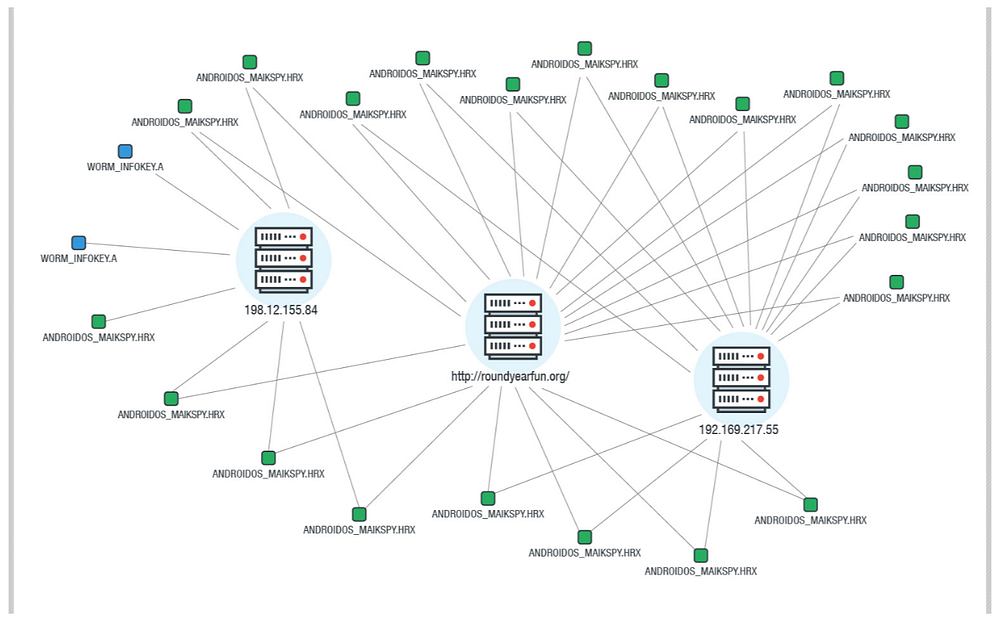
For more details around the connection between Round Year Fun and Maikspy, I highly recommend checking out Trend Micro’s post.
Here’s a visualization they put together that maps various relationships:
Round Year Fun (On Repeat)
The first time I encountered Round Year Fun was via a tweet linking to a game called Secret Admirer in October 2018.
I regularly scan Twitter search results for the phrases “Twitter bots” and “fake accounts” as these are areas which very much interest me. During the first couple weeks of 2019, the scans led me to Secret Admirer with far more frequency than previously. (I completed most of this post at that time; Twitter’s recent decision to permanently suspend my account has motivated me to highlight more of their negligence, hence I finally finished/published this one)
It was the tweet below that nudged me to finally take a closer look at the game:
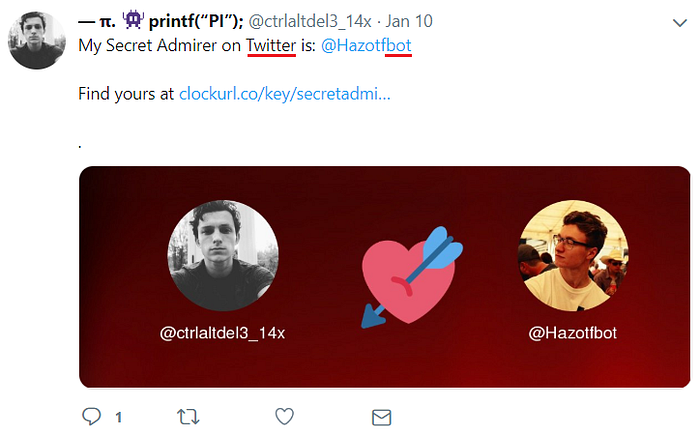
The exchange which followed (in Thai; between @ctrlaltdel3_14x and @Hazotfbot) — among other things — was a red flag:

Next I searched Twitter for the link (clockurl[.]co/key/secretadmirer) that was being shared (by what appeared to be inauthentic accounts).
The number of search results were sufficient to warrant further investigation, so, using Twitter’s API, I pulled recent tweets where said link appeared.
Below is a network graph representation of 2,100 Twitter accounts that tweeted, retweeted, or were mentioned in tweets which include “clockurl[.]co/key/secretadmirer” (tweets from Jan 4th to Jan 11th, 2019):

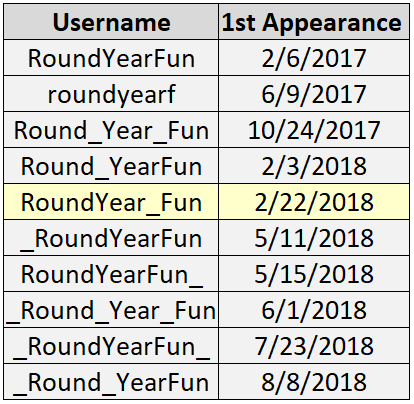
The @_Round_YearFun account (largest node above by far) — as you may have noticed — has a slightly different username than the @RoundYear_Fun account highlighted by Trend Micro in May 2018.
In fact, there have been at least 10 Twitter accounts, which, at some point, were operated by Round Year Fun, a gaming portal that currently reflects a tagline of “Fun Twitter games all year round” on their site:
Here’s an overview of those accounts (@RoundYear_Fun — yellow below — is the account that was highlighted by Trend Micro in May 2018; each of these 10 accounts have been suspended):
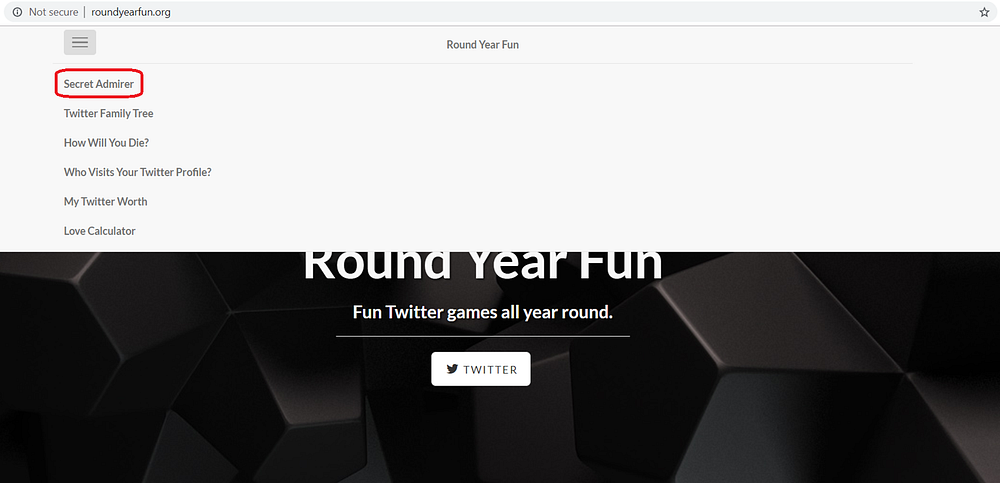
Round Year Fun’s site reflects 6 games:
- Secret Admirer (discussed earlier; this was the first Round Year Fun game I encountered)
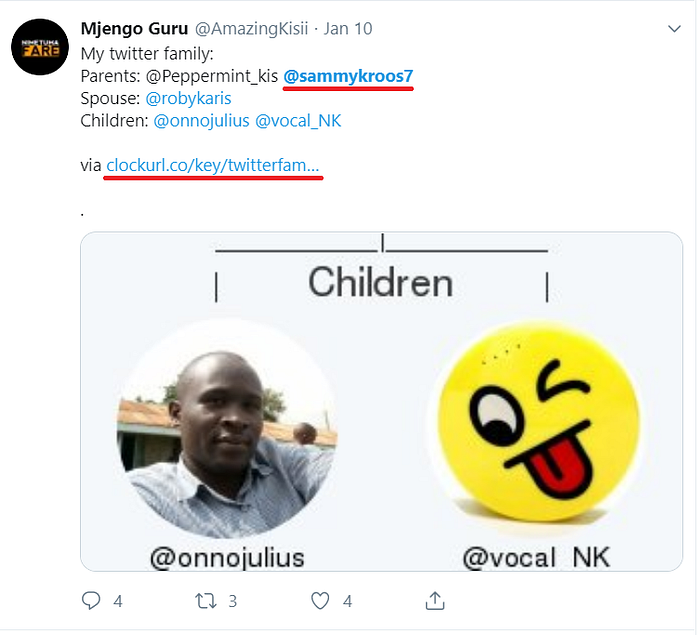
- Twitter Family Tree
- How Will You Die?
- Who Visits Your Twitter Profile?
- My Twitter Worth
- Love Calculator
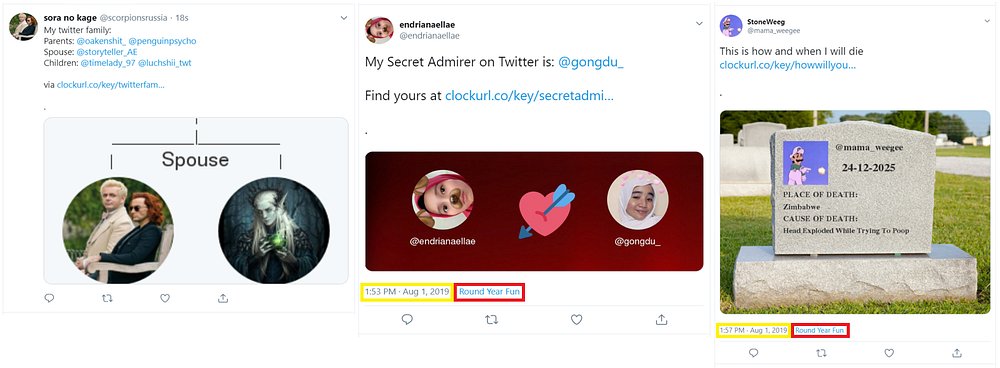
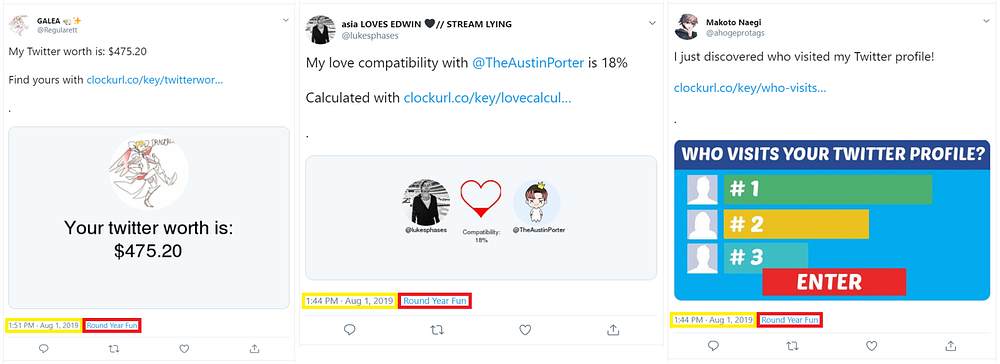
Earlier in this section I shared a network graph representation of 2,100 Twitter accounts (relating to the Secret Admirer game). Turns out Twitter is similarly littered with inauthentic accounts spamming links to the other Round Year Fun games as well (these examples are all from Aug 1st, 2019):
Here are the links being spammed across Twitter for each respective game:

Below is a network graph representation of 27,449 Twitter accounts that tweeted, retweeted, or were mentioned in tweets which include “clockurl[.]co” (tweets from Jan 5th to Jan 12th, 2019; NOTE: this is the same graph that appears atop this post):

ClockURL.co links on Twitter appear only in the context of Round Year Fun, hence pulling tweets which include “clockurl[.]co” (vs. “clockurl[.]co/key/secretadmirer”) extends our dataset beyond just the Secret Admirer game (such that additional Round Year Fun games are being captured as well):

Follow-For-Follow, Spam Accounts
Next I reviewed (profile) data obtained via Twitter’s API for the 27K+ accounts that appear in the “clockurl[.]co” graph/dataset.
Let’s take a closer look at one — namely, @sammykroos7:

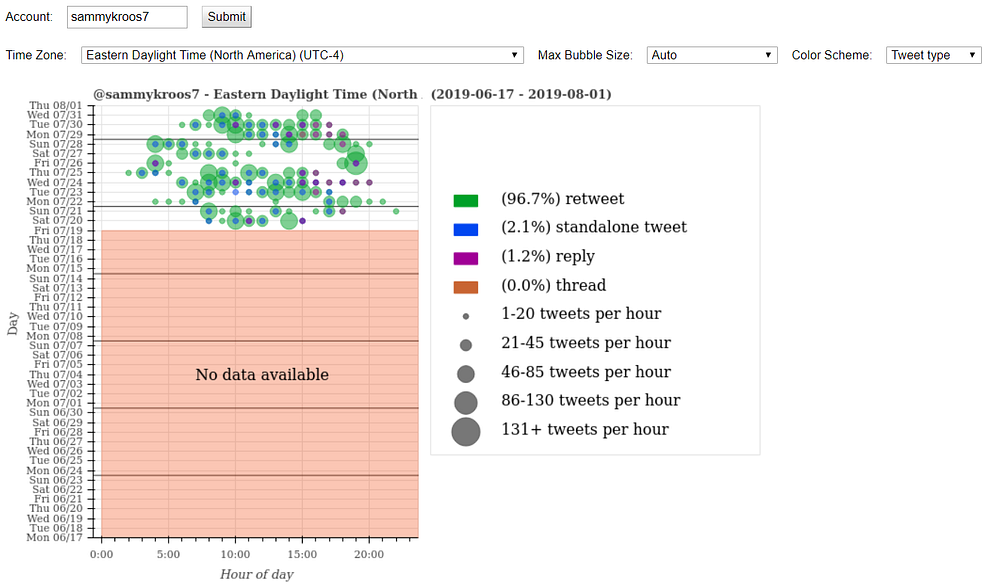
“kinqsammykroos” (@sammykroos7) has, on average, liked 645 tweets per day (while managing to tweet, on average, 208 times per day). This level of activity generally is indicative of a non-human behavior pattern.
Out of the account’s most recent 3.2K tweets, 97% are retweets. Additionally, there are several periods where the account churns out 86+ tweets per hour:
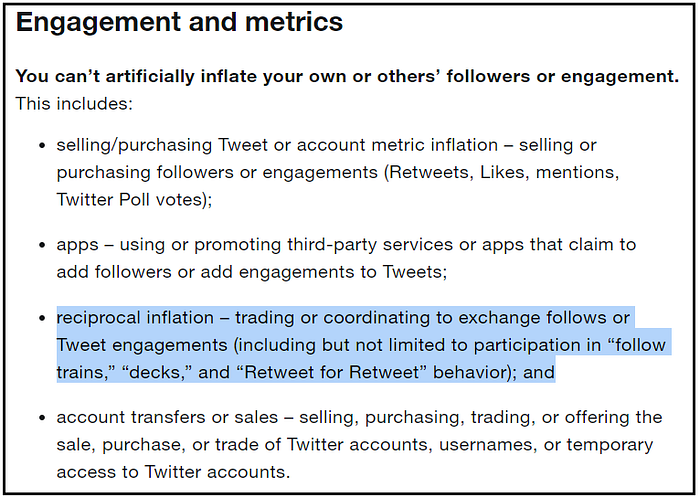
What does @sammykroos7 tend to retweet? Other inauthentic accounts that spam Twitter about gaining followers via “follow trains” (NOTE: this behavior violates Twitter Rules):

Here are the accounts most frequently retweeted by @sammykroos7 (red text where average tweets or likes per day for retweeted account exceeds 100):
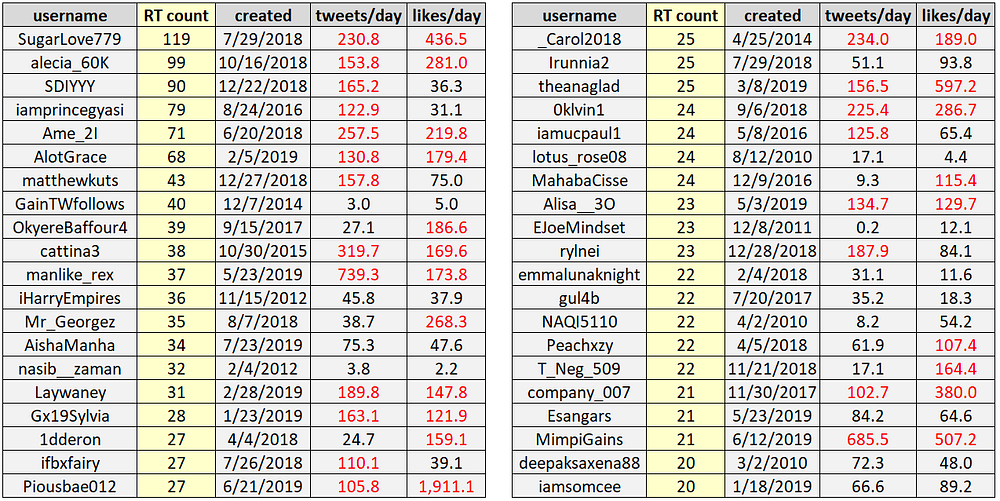
Many of the follow-for-follow accounts reflect having hundreds of thousands of “Followers” — once again, these accounts are in violation of Twitter Rules (and function to inflate platform metrics):
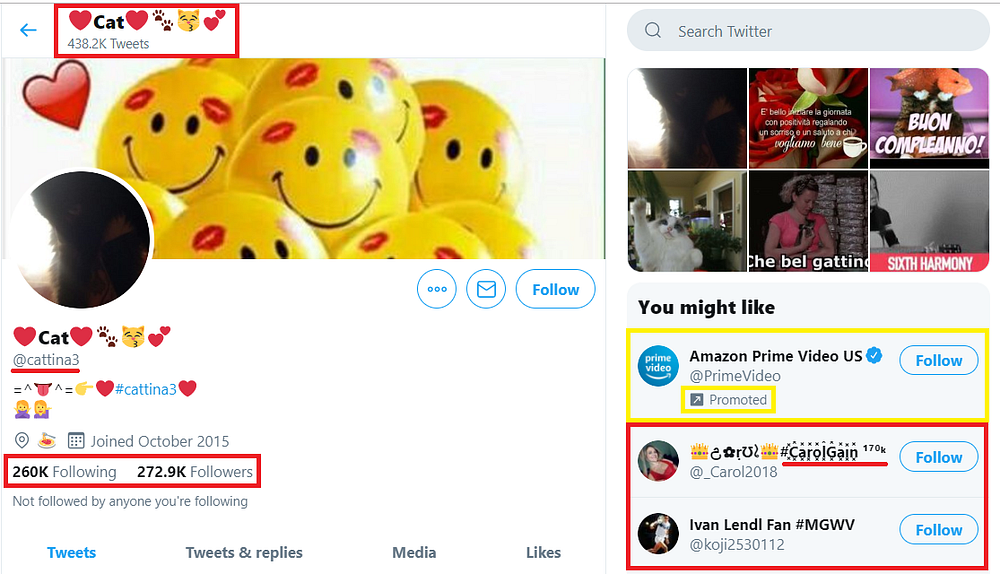
Twitter will likely suspend the @cattina3 account as a result of this post. What they won’t do, however, is suspend the hundreds of thousands of inauthentic accounts from “Cat’s” Following/Followers (and ones that round out this particular spam network, more broadly).
These type of follow-for-follow accounts/spam networks are rampant across Twitter and span several languages.
I’ll save that for a later post — now back to Maikspy!
Pure Negligence
As evidenced by Round Year Fun’s multiple usernames, apparently all that’s required to evade Twitter account suspension are underscores.
Twitter doesn’t allow sending “roundyearfun[.]org” via DM, hence they’re clearly aware of the issue:
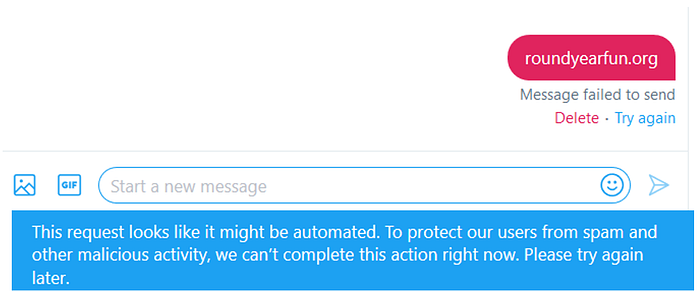
For some reason, however, Twitter can’t seem to rid their platform of inauthentic accounts spreading very nasty spyware — continuing to expose their users to data privacy risk.
Geoff Golberg is an NYC-based researcher (and entrepreneur) who is fascinated by graph visualization/network analysis — more specifically, when applied to social networks and blockchain activity. His experience spans structured finance, ad tech, and digital marketing/customer acquisition, both at startups and public companies. Geoff spends (far too much of) his time developing techniques and building tools to identify social media manipulation (of various flavors!)
